IED Jammer Workshop
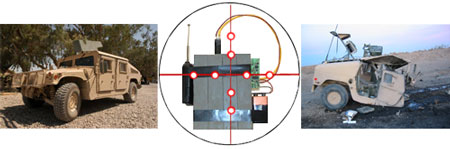
In order to comprehend IED Jamming technologies, one should know about how an IED Jammer works, its strengths, weaknesses, and data pertinent to the procurement and installation processes involved. Those responsible for deciding which system and specifications are necessary should be involved. Therefore, we offer an extensive workshop on RCIED defeat. IED Jammers that work to annihilate RCIED threats also known as Remote Controlled Improvised Explosive Devices vary in design, performance, and usage.
Our IED Jammer workshop takes into account that the tools of terrorism in the form of radio controlled IEDs are built and used like conventional weapons. Here at HSS, we understand that terrorists and insurgents are not made of military forces. They wear no uniform and are not identifiable as an army, and their budget to acquire weapons is not the same as that of a government sponsored military.
Terrorists employ unconventional methods of ambush attack patterns, where their intended targets can range from civilian non-combatants, women, children, political opponents, diplomatic targets, VIPs, as well as military forces and military targets. Their goals are to defeat their enemy through any means possible. This means they approve of roadside bombings of convoys, bombing targets in areas populated by civilians, wounding not only their enemies but bystanders, and gaining media attention to their causes while leaving death and disaster behind.
Our IED Jammer workshops explain how to defeat Terrorists remote controlled weaponry through Electronic Warfare. Terrorism is not the enemy. Terrorists are. Terrorism is the tactic employed by Terrorists. Once this is accepted, we then outline how our Electronic Warfare solutions, our IED Jammers, make up a greater portion of managing remote controlled weaponry, their composition, use, and how to defeat them.

RCIED weaponry vary in composition levels. But because our IED Jammers have several advantages when used against RCIEDs, we are able to explain and recommend the right solution to the many different scenarios involving RCIED weapons. IED weapons are unsophisticated in their construction, but all are directed against military forces, diplomatic corps, VIPs, guard tower and checkpoint installations be they military or police force, civilians and government agencies traveling in convoys through unstable regions where terrorists operate. IED weaponry involve ambush by Remote Controlled Improvised Explosive Devices or RCIEDs.
Seminar Origin:
After years of answering questions about IED Jammer performance and function, client expectations, and factors sought by security agencies, military and civilian think tanks, and those security resellers who market to their respective authorized government procurement agencies, HSS created the IED Jammer Workshop to explain all about the solutions to the destructive nature of RCIEDs or Remote Controlled Improvised Explosive Devices.
Similar to Guerrilla Warfare tactics, the RCIED threat is a modern day problem effecting many unstable regions throughout the world. Electronic Warfare using IED Jammers as a countermeasure against Remote Controlled Improvised Explosive Devices is the solution to a growing problem. Those who have experienced RCIED attacks now come to understand the necessity to inquire for a solution of this nature. These users understand the need to counter:
- insurgent attacks on political, diplomatic, and military advisers
- terrorist attacks on police agencies and civilian populations
- terrorist assassinations
Course Syllabus on IED Jammers from HSS
- The Definition of an IED
- How an IED is created: The composition of a Low Order Explosive in relationship to a High Order Explosive
- The Definition of RCIED as well as other IED weaponry
- Comprehension of enemy goals, methods of attack, their strengths, and weaknesses
- Defining enemy ambush tactics on the urban battlefield in populated and unpopulated regions
- Introduction to RF Jamming Systems
- Possible RF Triggers used to detonate RCIEDs
- The methods employed in a Defensive RF Jamming IED Jammer
- The BombJammer line of IED Jammers, performance attributes, and functionality
- Defensive RF Jamming under lab and field environments
- Frequently Asked Questions & Answers concerning IED Jammers
- Terminology of IED Jammers, Threats involved, and preferred RF Jamming Techniques
- System solutions from standard to customized applications
- Man Portable RF Jammers
- Vehicle Mountable RF Jammers for Convoy Protection
- Stationary RF Jammers for Government and high level security facilities including the Prison Jammer series
- Stadium environments for public safety
- Introduction of our PLL Stabilized BombJammer Technology
- Limited Demonstration of the Bomb Jammer series of IED Jammers
Question: Who generally attends an RCIED or IED Jammer workshop from HSS?
Answer: Government Users, Government Representatives, with a focus on Government and Military Officials, Government Contractors, Foreign Dignitaries, Law Enforcement Agents, Bomb Squad and Counter-Terror groups, and Authorized Resellers to Government agencies who resell or help in the procurement process of IED Jammers. Attendees must first register with proof of Government representation and or credentials indicating they represent the End User of IED Jammer technologies.
To learn more,
Contact Us for our IED Jammer Workshop time and locations.